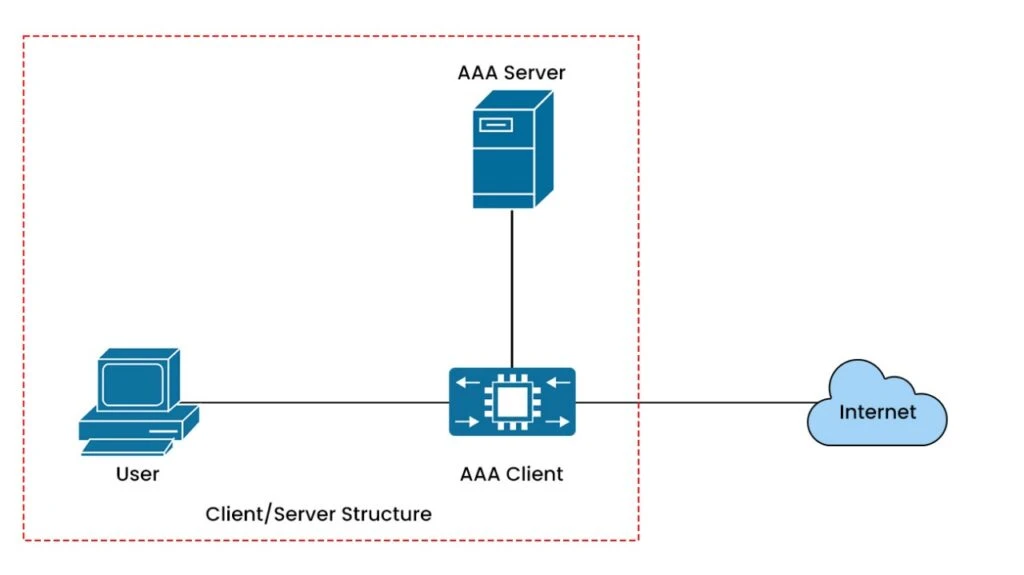
Telecom networks have changed significantly over the past decade. New access technologies, growing subscriber bases, and rising data demands have pushed operators to rethink how they manage and secure their infrastructure. At the center of that infrastructure sits the AAA server (Authentication, Authorization, and Accounting), the system that verifies who gets on the network, controls what they can do, and records everything that happens during their session.
For any subscriber-based network operator, all three are non-negotiable. Authentication makes sure the right users get in, authorization controls what they can actually do based on their plan, and accounting keeps track of usage so billing works properly. To understand in depth about what is AAA? Let’s step in with details.
Authentication (Who are you?)
AAA authentication is when a subscriber initiates a connection, the access device a NAS, BNG, or BRAS depending on the deployment sends an Access-Request to the AAA server with the subscriber’s credentials. The server checks them and returns either an Access-Accept or an Access-Reject.
For most fixed broadband deployments, this happens over RADIUS on UDP port 1812. The authentication method is typically PAP or CHAP. Nothing opens until this step completes. That makes the AAA server a hard dependency in the connection path. An undersized or unavailable AAA server doesn’t degrade the experience, it stops it entirely.
Authorization (What can you do?)
The approval and the policy travel together. When the AAA server says Yes, it also tells the access device exactly how to handle that subscriber speeds, quotas, and service tier.
- Upload and download bandwidth limits
- Service tier and QoS markings
- Data quota and cap rules
- Time-based or location-based access restrictions
This is where a subscriber’s purchased plan becomes actual network behavior. A wrong speed profile or a missing service flag shows up almost immediately, usually as a support ticket. Billing disputes trace back here too, when the service delivered doesn’t match what the subscriber was charged for.
Accounting (What did you do?)
Accounting-Start is sent when the session is established. Interim-Updates are sent periodically during long-running sessions. Accounting-Stop is sent at disconnect, with final byte counts and the disconnect reason.
These records feed billing, dispute resolution, and capacity planning. A gap in accounting data is never just a reporting problem. It either creates revenue leakage usage that goes unrecorded and unbilled or it forces a credit when a subscriber disputes a charge and there’s no record to dispute against.
RADIUS vs Diameter: How they differ and why both matter
Since the 1990s, RADIUS has been the default protocol for broadband and Wi-Fi AAA and for fixed-line operators, it remains the standard today. It’s stateless, runs over UDP, and is supported by every access device in the market. For operators running PPPoE or IPoE, RADIUS remains the standard protocol for subscriber authentication and it isn’t going anywhere. Alepo’s broadband AAA platform is built around this, with a consolidated RADIUS server handling authentication and accounting across fixed-line deployments, including FTTH.
Diameter is a different protocol built for a different context. LTE, VoLTE, and 5G mobile-core deployments use Diameter on interfaces like SWm, S6b, and Gx, where signaling volume and policy complexity exceed what RADIUS was designed to handle. It supports richer attribute sets, better error handling, and more complex session management requirements that didn’t exist when RADIUS was built.
Most operators don’t get to choose one or the other. Those running both fixed and mobile services need both protocols. The problem isn’t the protocols themselves it’s managing two separate AAA systems with two separate subscriber databases. That’s a maintenance gap that grows quietly until something breaks.
What actually fails in production
The protocol specs aren’t where deployments go wrong. These are the failure patterns that show up in real operator environments.
1. Ghost sessions
A subscriber disconnects without sending an Accounting-Stop a power cut, a device crash, or a link failure. The AAA server still shows the session as active. When that subscriber tries to reconnect, they’re blocked because the system thinks they’re already connected. Or a duplicate session builds alongside the original.
At scale, ghost sessions inflate active session counts, corrupt usage data, and generate support calls for lockouts that shouldn’t exist. Manual cleanup doesn’t work at volume. The platform has to detect and close them automatically, or the count keeps growing.
2. Authentication storms
After a power outage or a maintenance window, thousands of devices try to reconnect within a short window. The AAA server absorbs a flood of Access-Requests simultaneously. An undersized system starts queuing requests, then dropping them. Access devices retry on timeout which adds more load to a system already under pressure.
Most incidents reported as “AAA is down” are actually this scenario. The server isn’t down; it’s overwhelmed. The distinction matters because restarting it doesn’t fix the architecture.
3. Policy drift
A subscriber upgrades their plan or resets a quota. If the provisioning system pushes that change to the AAA server on a batch schedule instead of in real time, the subscriber gets the wrong policy until the next sync runs. It surfaces as a speed complaint or a billing question. The root cause is the integration between provisioning and AAA, not the AAA platform itself.
Also Read: How Wi-Fi Offload Tackles Cellular Network Congestion
What a production-grade AAA platform needs
Not every AAA deployment is built for these realities. The gap between a system that validates credentials and one that manages the full session lifecycle at operator scale is larger than it looks from the outside.
- Unified protocol coverage
RADIUS for broadband and Wi-Fi. Diameter for mobile core. Both managed from a single platform with a single subscriber database. Separate stacks create consistency problems that don’t stay separate. - Automatic ghost session resolution
Not flagging for manual review, actually closing them. The distinction matters at ten thousand sessions versus ten. - Active load distribution
Traffic spread across multiple AAA instances with no single point of failure sitting in the path of every subscriber connection. - Migration support
Operators replacing legacy CPAR-based systems need coexistence patterns that keep services running during transition, not a hard cutover that creates a maintenance window.
The infrastructure that’s easy to ignore until it isn’t
Nobody thinks about AAA until the infrastructure is compromised. It runs quietly under every subscriber session, never asking for attention, never showing up in a board report. So upgrades get pushed, old infrastructure gets another year of life, and accounting gaps get ignored because no ticket was raised.
Then a storm hits. Or a billing audit flags a six-month discrepancy. Or a subscriber calls in furious about a lockout that traces back to a ghost session nobody caught. By that point, the problem isn’t new, it just finally got loud enough to notice.
The operators who avoid those situations aren’t necessarily running the newest equipment. They just stopped treating AAA as someone else’s problem to deal with later.
FAQs
- What is an AAA server in telecom?
An AAA server is a centralized system that authenticates subscribers, applies service policies based on their account, and records session data for billing and analytics. It sits in the path of every subscriber connection on the network.
- What does AAA stand for?
Authentication, Authorization, and Accounting. Authentication verifies the subscriber’s identity. Authorization defines what they’re permitted to do on the network. Accounting records what actually happens during the session.
- Is AAA the same as a RADIUS server?
Not exactly. AAA describes the set of functions. RADIUS is the most common protocol used to implement those functions in broadband and Wi-Fi networks. A RADIUS server is a typical AAA implementation but AAA can also run over Diameter in mobile-core environments.
- What’s the difference between RADIUS and Diameter?
RADIUS is stateless, runs over UDP, and has been the broadband standard for decades. Diameter was built for higher-scale mobile networks LTE and 5G where signaling volume and policy complexity exceed what RADIUS handles. Both protocols are widely deployed; operators running fixed and mobile services typically need both.
- Why does accounting matter beyond billing?
Accounting records are the basis for dispute resolution, capacity planning, and auditing. Gaps in that data create two problems: unbilled usage that becomes revenue leakage, and missing records that make it impossible to verify a charge a subscriber disputes.
- What causes ghost sessions?
A subscriber disconnects without the network receiving an Accounting-Stop message usually because of a device crash, power failure, or abrupt link drop. The AAA server retains the session as active. Without automatic detection and cleanup, ghost sessions accumulate and cause lockouts on reconnect.
- What systems connect to an AAA server?
Typically NAS, BNG, and BRAS devices; Wi-Fi controllers; mobile core elements; provisioning and CRM systems; and billing or analytics platforms.



